FAQs
Using the Training Arcade® Game Authoring Tool
Support
Standard Support Policy for Current Subscribers:
- Monday – Friday, 9:00 a.m. – 5:00 p.m. Eastern Time, excluding bank holidays.
- One business day response time on most questions.
- Email us please at support@thetrainingarcade.com
Creating Games
1. If the original invite link has expired, you won’t be able to use it again (email links are one time use.)
2. Click the reset password link.
3. Have your Admin remove and re-add you
4. Write to support@thetrainingarcade.com; let us know the URL of your Training Arcade domain.
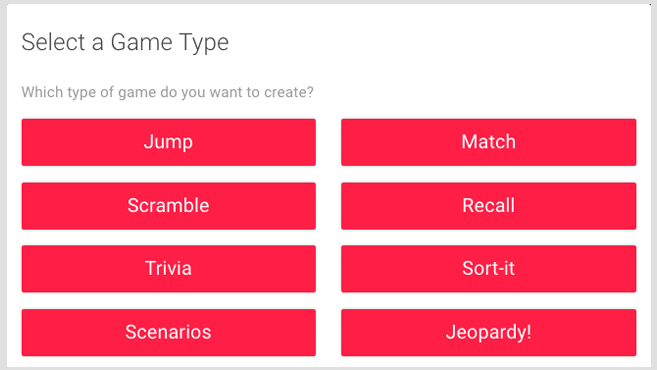
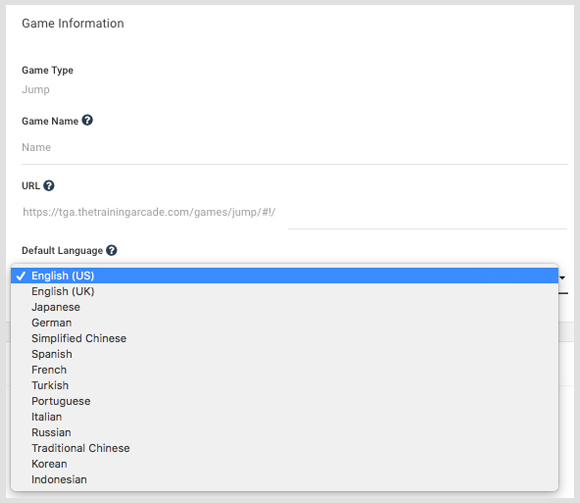
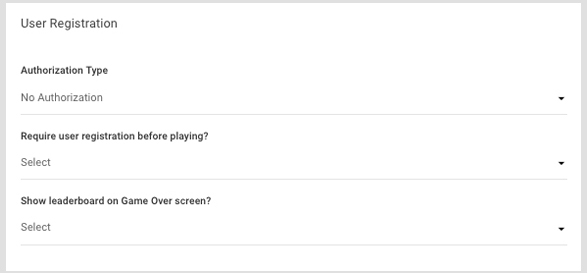
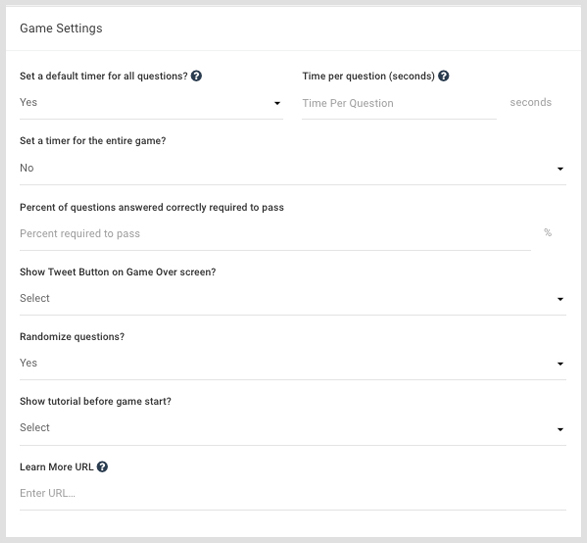
The Training Arcade® allows anyone to create a game in under 30 minutes (no coding necessary). This game builder is remarkably intuitive and can be managed with drop downs, uploads, and type-in fields. Below are several screenshots showcasing the steps required to create a game.
Step 1 – Choose your basic game information
Step 2 – Define global game settings
Step 3 – Identify SSO integration, user registration, and leaderboard display
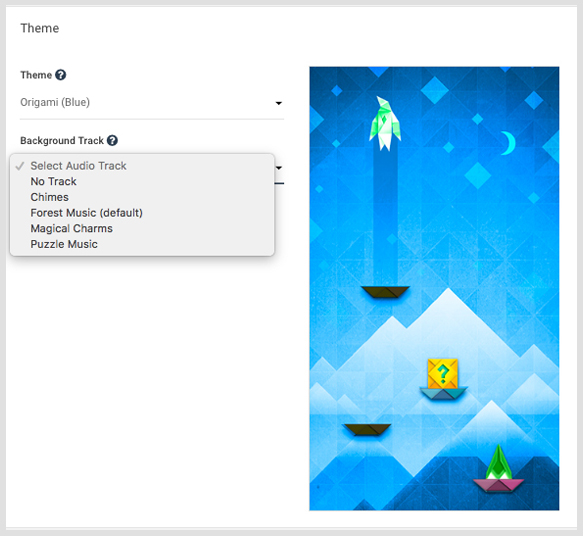
Step 4 – Pick from visual templates and audio tracks
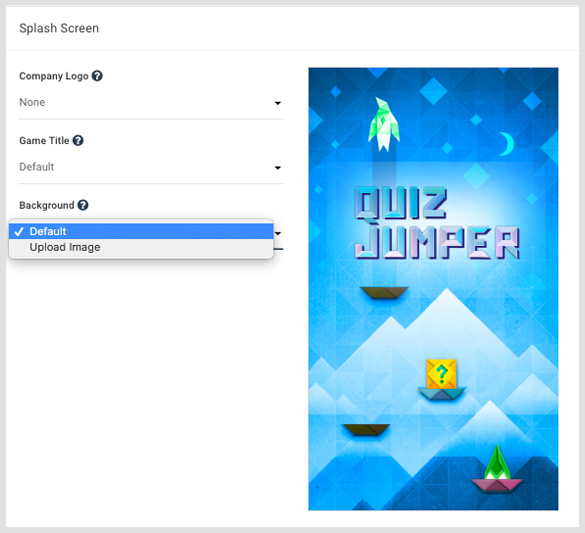
Step 5 – Customize splash screen with logo, title, images, etc.
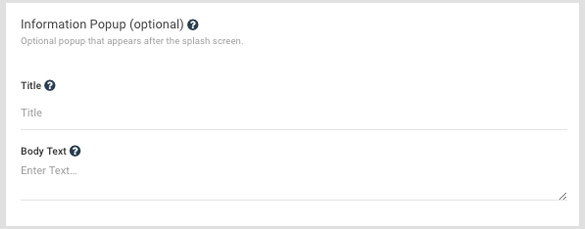
Step 6 – Write pop-up information to provide players with context before they play
the game.
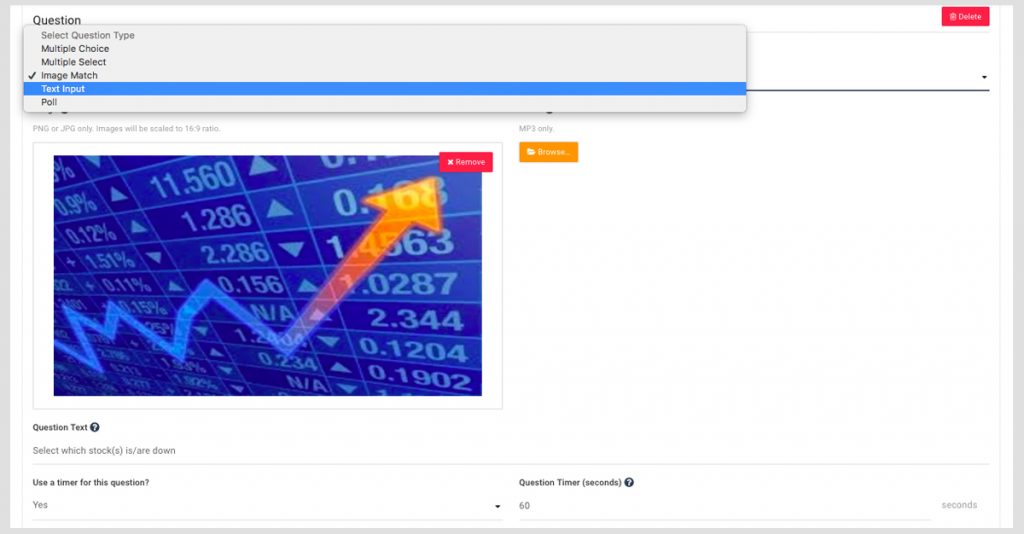
Step 7 – Start adding questions (choosing from 5 types), uploading media, identifying right/wrong answers, and writing corrective feedback
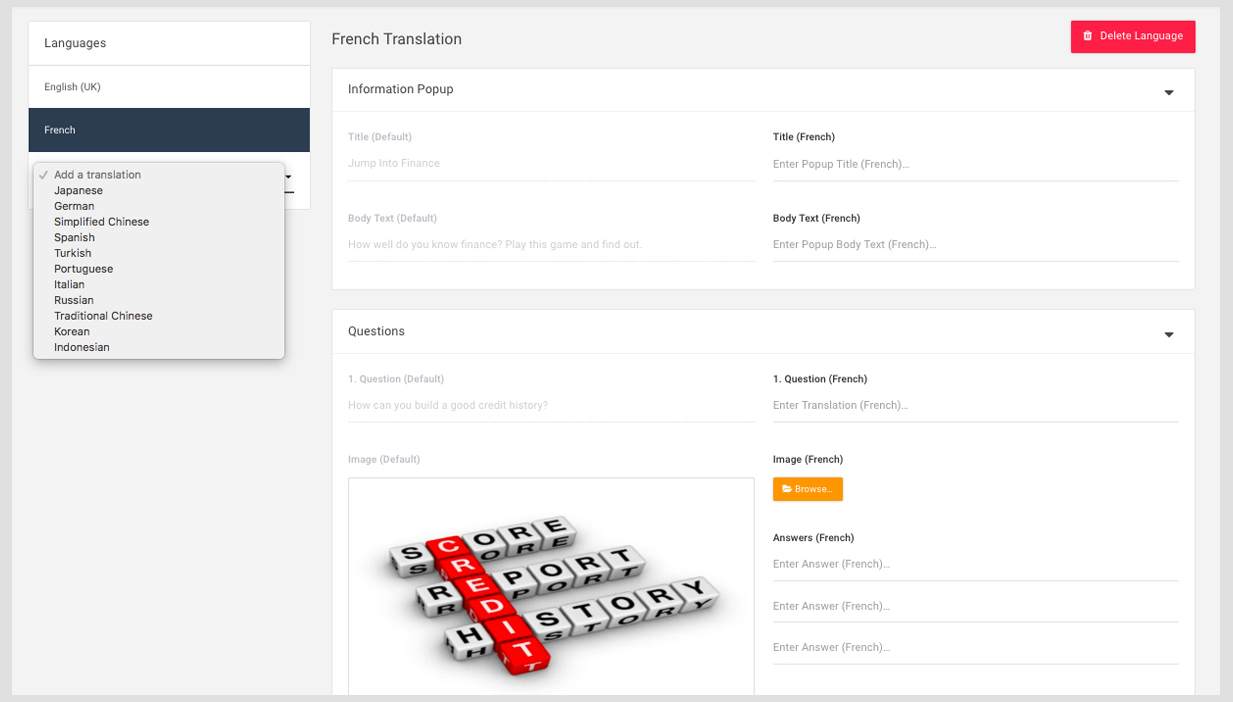
Step 8 – Translate game into 16 other languages
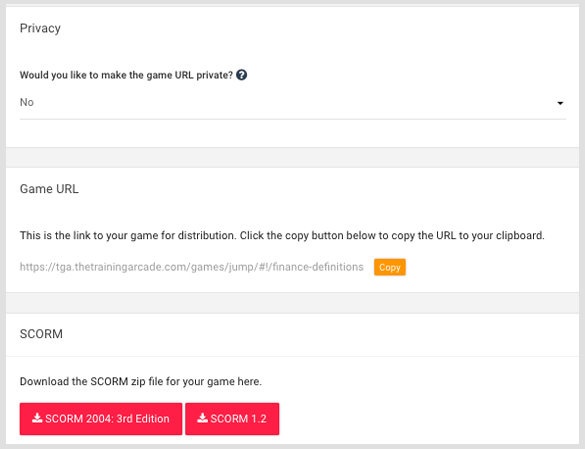
Step 9 – Publish game
The Training Arcade® includes 6 Question Types
- Multiple choice: the user selects a single correct answer from a selection.
- Multi-select: the user must select all of the correct answers from incorrect answers.
- Image select: multiple select, but with pictures
- Text Input: the user must type in the correct answer (it’s not case sensitive and you can add multiple spelling variations).
- Polling: you can create a Poll to understand which options are the most popular.
- Info Card: you can add text, videos, and pictures. This is a versatile “question type” which can serve many purposes.
When learners receive corrective feedback right away they are more likely to remember that feedback later on. So, The Training Arcade® makes it easy to give (or get) immediate feedback. For best results, we encourage you to provide feedback for both correct and incorrect answers, adding useful context to each of your points.
You can create as many games as you want with any of The Training Arcade® game mechanics in your subscription.
Below is a list of multimedia file types that can be uploaded into The Training Arcade®
- Image: JPEG or PNG
- Audio: MP3
- Video: MP4 (30MB limit) or link to any URL
The ratio for all images in The Training Arcade® is 16:9. We suggest using this tool https://www.calculatorsoup.com/calculators/math/ratios.php to help you adjust your image accordingly.
The Training Arcade® games can all be published as SCORM 2004: 3rd Edition and SCORM 1.2 packages for easy integration into the majority of LMS.
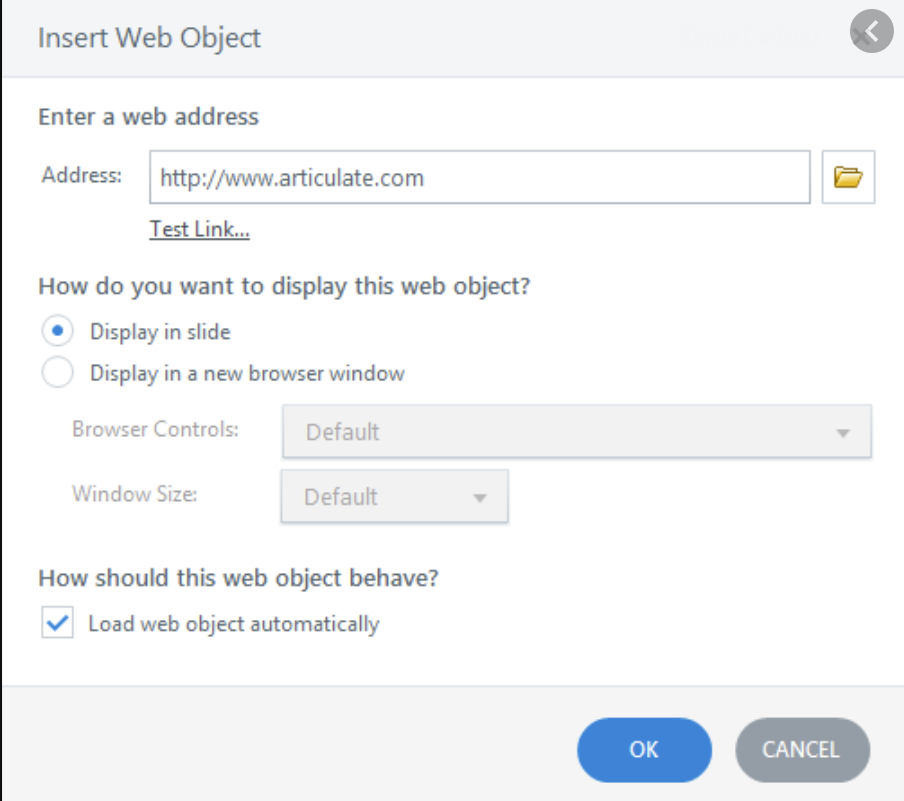
You can integrate The Training Arcade® into PowerPoint, Storyline, Captivate, Lectora, and other eLearning authoring tools as a web object.
The Training Arcade® games are currently available in 20 languages:
- English (US)
- English (UK)
- Spanish
- French
- German
- Greek
- Italian
- Russian
- Turkish
- Portuguese
- Traditional Chinese
- Simplified Chinese
- Korean
- Japanese
- Indonesian
- Thai (Match Game only)
- Hindi
- Czech
- Polish
- Dutch
There will be additional languages added in the future.
The sky’s the limit. Subscribers use The Training Arcade® to build training and reinforcement games focused on new-employee onboarding, sales and product training, leadership development, safety, security, compliance, systems & processes, customer service, and many other training topics.
Most subscribers utilize The Training Arcade® games for
- eLearning / mLearning
- Instructor Led Training
- Live Events
Yes. If you like our games but want a custom design to fit your brand, we have two options:
Basic – ($2,000 – $6,000) per game. This includes color updates to one of our existing backgrounds or implementation of art you supply based on our specifications, font updates, and new or edited characters / icons.
Advanced – ($10,000 – $14,000) per game. This includes custom backgrounds, font updates, new characters / icons, alternative button shapes, additional sound fx, and additional music tracks.
Take your game link when ready and embed it as a “web object”. You would need to find the web object on your side in the course. The platform allows you to “add a web object” on a slide in the course. Then paste your game link into the field and our game will then play on the specific slide. Here’s an example:
For the JEOPARDY!® and Trivia games that are used in a Virtual or Live Instructor mode, we recommend having no more than 200 players on a call or playing simultaneously. For any game playing in standard mode there is no issue with bandwidth.
Sure! Each and every game can be embedded into a learning course or on a website. Once a game is built in the system, click on the Publish tab which will give you the option to copy the game URL link and paste it into a course or input your site size requirements and the system will generate an embed code.
We can help with graphics as a custom Scope of Work. The graphics can range from live actors to animated characters and everything in between. We can create any idea you may have or our team can come up with ideas and present the SOW for review. One of our partners, ELB Learning has a huge asset library. Vyond is great for creating videos.
Yes, you can use a PowerPoint plugin that will allow you to play a game at any point in your presentation. Watch this video to learn more. Or turn your PowerPoint into a game, read more here.
Well, it depends of course. It depends on which game you select and whether you are still developing your content. If you have all your training content and visual assets all ready to go, building and launching the game takes minutes.
As of now, we’re not 508 Compliant but we are working on it.
Yes, we are compatible with most LMSs but the only SCORM data that passes to an LMS is who the player is, high score and level of completion. All the rest of (the more detailed data) can be viewed in our dashboard.
The Unique Player Count is the sum of registered players and anonymous players. A registered player is a player for whom sufficient personal data is provided for an individual’s actions to be tracked across multiple gameplay sessions (for example, name and email address). A registered player may play an unlimited number of games during the Subscription Term and is counted only once toward the Subscriber’s purchased player threshold during the Term. An anonymous player is a player for whom there is insufficient personal data to track an individual’s actions across multiple gameplay sessions. For anonymous play, each gameplay session counts as a unique player towards the Subscriber’s purchased player threshold.
Overview of Data, Security, and Privacy Policies
Check options at our Analytics section.
SECURITY
The Training Arcade® is used by some of the most highly regulated industries and corporations. As a result, we take security very seriously. Below is an overview of our protocols.
ACCESS CONTROL
TGA has defined processes for access management (e.g. provisioning accounts for users, limiting user access based on the principle of least privilege, terminating access and periodic access certification). TGA access to client data is governed by our Privacy Policy. The Training Arcade® resides on AWS. We maintain strong password configuration requirements (high character count, include lowercase and uppercase alphabetic characters, numbers and symbols). and require multi-factor authentication to further secure the environment.
Passwords expire at least every 90 days and are encrypted at rest and in transit, using industry-standard information security encryption algorithms. For customer data on The Training Arcade® a protocol is in place to prevent connectivity between two sets of data. Specifically, every customer has a unique subdomain and we have a software protocol in place to prevent connectivity to data stored under a subdomain to which a customer is not authorized access.
ASSET MANAGEMENT
For systems which have access to Client Data, a separation of duties process is in place for approving and implementing access with sponsorship and duration documented. Access to Client Data is limited to providing the service and in accordance with our Privacy Policy. Employees and contractors are assigned unique user accounts to access Client Data, systems and/or applications. We maintain a Data Classification policy that includes security requirements based on the classification of the data. We do not maintain any physical assets or servers in our offices. All information is stored within Amazon Web Services EC2 instances and RDS databases.
BUSINESS CONTINUITY
We have a Business Continuity Plan (BCP) and a Disaster Recovery Plan (DRP). The plans are part of a broader context that include Security, IT, Personnel and company operations. Specifically the BCP & DRP cover handling both disruptions (environmental, electrical, civic disruption, etc.) and destruction (fire, flood, explosion, earth movement, etc.) at our physical locations and the AWS data centers we use to deliver services. The plans include information on backup infrastructure and procedures, chain of command and communications to employees and clients, and overall system recovery. The annual test of our BCP and DRP was completed March, 2019. All clients using The Training Arcade® are notified when there are scheduled or unexpected interruptions to the service.
COMPLIANCE
For more information on the topics below, please refer to our Privacy Policy. We do not store, transmit, process or access Client Data, systems and/or applications from outside the United States. There are individuals responsible for ensuring compliance with Privacy, Regulatory, Legal and Security requirements.
CRYPTOGRAPHY
All non-public data is encrypted in transit using TLS and our databases are encrypted at rest. Client Data is encrypted in transit over public networks. Remote access connections into our network occur over an encrypted tunnel (e.g. VPN). Logins and data transfers are secured with encryption for cloud connections (e.g. HTTPS, SFTP, etc.). Wireless networks are required to be encrypted in accordance with industry standards.
HUMAN RESOURCES
We conduct background checks on employees in accordance with local, state and federal laws. We expand this to third parties and contract workers on a case-by-case basis depending on the specific engagement. We expand the scope of the background check when the situation requires it (e.g. our work in
banking/financial institutions).
INFORMATION SECURITY
We manage risk via policies governing web security, application security, server/IT security, business continuity, disaster recovery, change control, The Training Arcade® privacy policy & terms of use, The Training Arcade® subscription agreement, and The Training Arcade® guidelines and restrictions. Collectively, we review these policies at least annually. All confidential information, otherwise known as PII (personal identifiable information), is restricted to TGA administrators only. This includes access, handling, and destruction of data. Admin access is reviewed and granted by TGA super Admin on a monthly basis and ad hoc as required. TGA employs a third party security firm that conducts annual training to team members based on their role and relative access to data and confidential data. A small group of administrators receives additional training related to best practices and the evolving threat landscape. There is a process to identify, monitor, track, and remediate all identified risks and vulnerabilities on an ongoing basis.
INFORMATION SECURITY INCIDENT MANAGEMENT
We have an Incident Management Policy and an Incident Management team assigned to respond to security incidents. TGA has support agents that operate during business days, during business hours (Monday through Friday 9:00 AM to 6:00 PM EST). TGA also employs team members who are on call 24/7 and are notified of system outages, security events, and other major alerts. If required for the scope of work with Enterprise Learning we can employ dedicated support staff to meet customer requirements.
OPERATIONS SECURITY
When an issue is identified, TGA personnel log it in our task management system and assign it to the appropriate technical personal with priority level, description, and requested due date. Technical staff accepts the ticket by marking it as in progress. Once resolved, the ticket is sent back to the reporter who provides a quality assurance function and closes the ticket when satisfied. All updates and changes are deployed in commits and merged into the staging or production instances for deployment when appropriate. Production deployments do not occur on Fridays or Holidays except in the case of emergencies and critical
updates. Backups of systems and data are performed daily.
ORGANIZATION OF INFORMATION SECURITY
We have an Information Security Policy and an Information Security team with defined Privacy and Security roles and responsibilities. Our information Security group maintain contacts with Information Security special interest groups, specialist security forums, and professional associations (i.e. ISACA, CSIRT,
(ISC)2, etc.)
PHYSICAL & ENVIRONMENTAL SECURITY
TGA is a US-based company that does not store any client data on its premises. Client Data resides in a secure data center and AWS facilities maintain environmental controls.
SYSTEM ACQUISITION, DEVELOPMENT
Change Control: TGA employs formal change control process. Changes are monitored throughout the implementation process to ensure success. The process is spearheaded/owned by the product owner, and managed via stand-ups, sprint cycles, and backlog. Appropriate segregation of duties is maintained between change approvals and change implementation. Approvals are obtained for Emergency changes. There are separate development, test, and production environments. We ensure that client production data is not used in development, staging, or testing / QA environments. We have a vulnerability management program that includes remediation of vulnerabilities identified in network and application security tests.
We maintain policies related to business continuity and disaster recovery alongside policies that govern security, privacy, IT, company processes, software development and human resources. Our Incident Response Policy and Service Level Agreement articulate the communication and escalation process in the event of any downtime (including details of Maximum Tolerable Downtime, Recovery Time Objective, Recovery Point Objective and Response Time, along with other related details).
The Training Arcade® is a multi tenant SAAS product. That said, we never sell or share client data with any 3rd party. The Training Arcade® team will only access your account to provide customer support or to enforce our terms of use.
99% of our customers utilize our multi tenant system (including governments, global financial institutions, big pharmaceutical and other highly regulated companies). We do have a handful of clients that are on dedicated single tenant branches that we can scope/propose on a case-by-case basis if needed.
There are no geo-blocking concerns. As long as your players have an internet connection they will be able to play the games. We have global companies that use the platform.